Digital Transformation
More Details
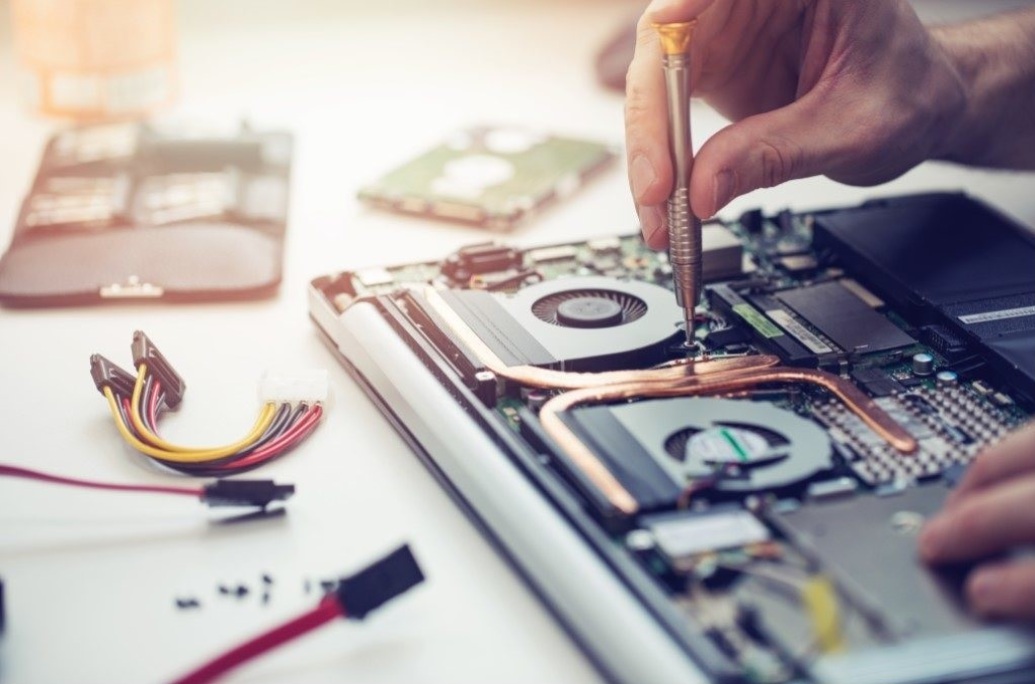
HardWare & Maintinance
More Details
Advanced Soluations
More DetailsProjects





Let's work together
Phone
+20233386591
+201093261526
info@cserve-egypt.com
Location
3 Ibn Elwaleed St. Dokki Giza Egypt
9 Meriet St. Tahrir Sq. Cairo Egypt
About
Who We Are ?
Founded in 1992, Compu Serve has specialized since its inception in the field of information technology providing integrated solutions to its customers starting from government sector, business companies, and strategic accounts, ending with private sector companies and individuals.
Vision
One of the main professional companies to provide integrated technological solutions in Egypt, Middle East, and North Africa.
Mission
To provide effective and efficient technology solutions to clients followed by an outstanding technical support and services.
Strategy
Transferring the world’s most cutting-edge technology solutions and products to customers with total commitment of successful implementations and continuous support, and this will be achieved by clear understanding of customer’s requirements and specifying their exact business needs which leads to an effective and efficient solution that should facilitate their business and work environment.
Success Partners
Digital Transformation
Backlog Conversion Services
More Details
Enterprice Content Managment
More Details
Digital Treanformation Consultation
More DetailsAdvanced Soluation

Video surveillance systems
More Details
Garage door systems
More Details
Access control systems
More Details
Vehicle recognition systems
More Details
Pedestrian traffic gates
More Details
Metal and bag detector gates
More Details
Under vehicle scanning systems
More Details
Traffic barrier systems
More Details
Queuing system
More Details